Secure WordPress hosting: The security responsibilities every hosting provider should own in 2026

- Secure WordPress hosting means explicitly owning the infrastructure layer: WAF, DDoS protection, server isolation, origin-layer filtering, and offsite backup architecture with malware scanning.
- The median time to exploit a newly disclosed WordPress vulnerability is five hours. Hosting providers that aren’t plugged into real-time threat intelligence networks are structurally behind on response time.
- Ecosystem relationships, active intelligence-sharing with security companies, are a meaningful operational differentiator for hosting companies.
- Backup is security. Offsite storage, malware scanning before restoration, and selective recovery options are the standard now.
- When hosting providers extend into application-layer security (plugin vulnerability monitoring or virtual patching), they strengthen agency care plans rather than compete with them.
- Security responsibility is shared. Hosts own the infrastructure. Agencies own the application and the client relationship. The failure mode is both sides assuming the other has it covered.
There’s a question that tends to surface after every major WordPress hack, usually in a support ticket or a tense client call: who was supposed to handle that?
The honest answer is that nobody’s quite sure. Agencies assume hosting providers cover the infrastructure. Hosting providers assume agencies are managing updates and access control. Clients assume everyone else has it handled. And in the gaps between these assumptions, websites get compromised.
The root of the problem is ambiguity. Responsibility only transfers when it’s explicitly accepted. If a hosting company hasn’t clearly defined what they own, then from a practical standpoint, they haven’t accepted accountability at all, regardless of what an agency assumed when they signed up.
This matters a lot for hosting providers right now. Because the question agencies are increasingly asking when they evaluate a hosting partner isn’t just about speed or price. It’s simpler than that:
If something goes wrong, are you in this with us?
The hosting providers that can answer yes, and back it up operationally, are pulling ahead. The ones that can’t are becoming line items that agencies plan to replace.
So, what does secure WordPress hosting look like in 2026?
1. Infrastructure security: what a secure WordPress host should offer
The foundation of everything is infrastructure, and this is where the clearest ownership line exists.
Agencies should not be configuring WAF rules. They should not be hardening Linux servers or determining whether a network anomaly is a DDoS attempt or a traffic spike. That’s not their domain, and leaving it ambiguous is a sign that a hosting provider hasn’t thought carefully about what they’re selling.
What the infrastructure layer looks like when it’s properly owned:
Network-layer protection: A web application firewall is not an add-on. WAF coverage, OWASP Top 10 protection, and DDoS mitigation are baseline expectations in 2026. With automated scanning tools and AI-driven exploitation now compressing the time between vulnerability disclosure and active attack, a hosting provider without this layer isn’t a viable option for agencies managing client websites at scale.
Origin-layer filtering: Network-edge filtering blocks what it can see at the perimeter. Origin-layer analysis adds context to what gets through. Layered coverage means anything that clears the first line faces a second. A single-layer approach isn’t defense in depth; it’s a single point of failure.
Server isolation: Without proper containerization, one compromised site becomes a vector into every other site sharing that server. Hosting providers that haven’t solved for tenant isolation aren’t just putting individual customers at risk; they’re putting entire agency portfolios at risk.
Backup architecture: Security and backup are the same conversation. Backups stored on the same server as the site they protect are a liability that looks like insurance until the moment it becomes important. Offsite, geographically distributed backup storage is the standard. Equally important is malware scanning before restoration. Restoring from a backup that was already infected before the incident is a surprisingly common failure mode, and one that an honest hosting provider should be actively preventing.
The underlying principle across all of this: agencies exist to build and manage websites, not to manage infrastructure. Hosting providers who make infrastructure a burden their customers have to think about have misunderstood their own value proposition.
2. Threat intelligence: why WordPress hosting providers need security ecosystem relationships
This is the layer that separates hosting providers who are serious about security from those who have bought the right tools but operate in isolation.
WordPress security is ecosystem-driven. Vulnerabilities are discovered by researchers, disclosed to vendors, tracked by intelligence platforms, and exploited, often within hours. According to Patchstack, the average time between a vulnerability disclosure and active exploitation is now around five hours. And that window is closing every year.
A hosting provider that finds out about a zero-day at the same time their customers do, by reading about it online, is already behind. The only way to be ahead of that curve is to have direct relationships with the companies working the intelligence side of the ecosystem.
What this looks like operationally: shared communication channels with security vendors, direct lines when something suspicious emerges and coordinated response when a zero-day hits. When a critical exploit surfaces, the hosting providers with ecosystem relationships can act within the hour. In contrast, the ones operating in isolation are reactive by default. They’re responding to the same public disclosure everyone else is reading, which means their customers are exposed to the same window everyone else’s customers are exposed to.
Security today is collaborative, not isolated. Zero-days don’t target specific hosting providers; they target WordPress at scale. The response has to match that scale, which means hosting providers need to be plugged into the networks where that information flows.
3. WordPress incident response: how should you operate when sites go down
Infrastructure and threat intelligence matter before an incident. This layer is about what happens during one, and it’s where the gap between hosting providers who’ve genuinely thought about security and those who treat it as a marketing checkbox becomes impossible to hide.
The most common failure is that many hosting providers have never defined their incident response process at all. When something breaks, they improvise, and agencies managing client livelihoods are left waiting for answers while the clock runs.
Hosting providers who take this seriously build it out in advance:
- A documented disaster recovery process with a tested sequence. It should include what gets checked first, who handles what internally, what the expected resolution timeline looks like, and what visibility customers have throughout. Writing it down forces the hard questions before they arise under pressure.
- When an incident hits, the hosting provider should be reaching out to affected customers, not waiting to be contacted. Providers plugged into security intelligence networks can often get ahead of public disclosure entirely with proactive customer communication, giving agencies a response window that others don’t have.
- Selective backup restoration. A full site restore is rarely what’s needed. Hosting providers who’ve invested in granular restoration tooling save agencies significant time and reduce the risk of restoring malware alongside clean data. This requires thinking about backup architecture with recovery in mind, not just storage.
Agencies are managing other people’s businesses. When a client’s site goes down, they need a hosting partner who has already thought through the recovery process, one who can tell them what’s happening and the timeline looks like. Hosting providers who can offer that aren’t just technically capable. They’re genuinely useful partners, and that distinction drives retention more reliably than any infrastructure feature.
Bonus: WordPress care plans as a revenue stream
Security infrastructure is the foundation. But for hosting providers willing to go one step further, there’s a direct commercial opportunity sitting on top of it.
WordPress-related issues, such as outdated plugins, failed updates, and performance degradation, are among the most common support tickets hosting providers handle. Most of that volume is reactive, unpaid, and expensive to service. The same problem that’s draining support resources is also the one customers would pay to have proactively managed.
Some hosting providers have already made this shift. They’ve turned WordPress maintenance into a structured, monetized service tier layered on top of their hosting plans. The model covers what most WordPress site owners need, including plugin, theme and core updates; security and downtime monitoring; offsite backups; and regular maintenance reports.
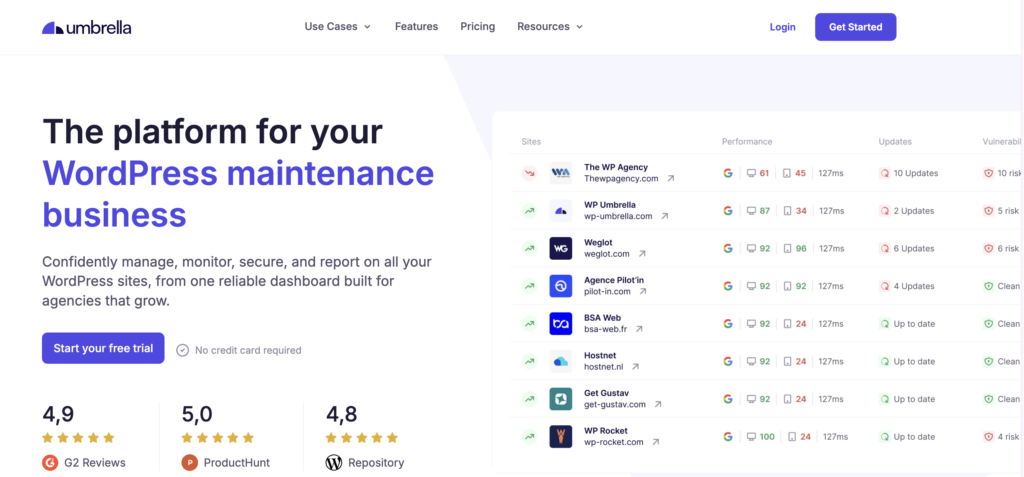
With the right tooling, rolling out a WordPress care service doesn’t require touching hosting infrastructure or making a significant upfront investment. The key is a platform that centralizes site management, automates safe updates, handles offsite backups independently of the hosting environment, and generates client-facing reports that communicate value month after month.
For hosting providers, this is where the security conversation becomes a growth conversation. The infrastructure layer earns trust. The care plan layer earns recurring revenue. They’re not separate products but a natural progression, and the hosting providers who’ve connected them are opening a revenue stream that compounds with their existing customer base.
You might also like: How Hostnet added 2000+ WordPress maintenance plans & opened a new revenue stream.
How WordPress security should be divided between host and agency
Hosting providers own the infrastructure: the network and origin layers, server isolation, backup architecture, threat intelligence, and incident response. Agencies own the application: plugin and theme management, admin access control, client education, and care plan delivery.
The failure mode isn’t that one side is irresponsible. It’s that both sides assumed the other one had it. When a website gets compromised, and nobody’s quite sure who was supposed to prevent it, that’s almost always the story underneath.
FAQs about secure WordPress hosting
At minimum: a web application firewall (WAF), DDoS mitigation, server-level malware scanning, tenant isolation between hosted sites, and offsite backup storage with malware scanning before restoration. Beyond that, serious hosting providers also offer origin-layer filtering, active relationships with vulnerability intelligence platforms, and documented incident response processes. If a hosting provider can’t clearly explain what they cover at each of these layers, that ambiguity is itself a risk signal.
A hosting provider’s WAF operates at the network or server level, filtering traffic before it reaches the application. It’s effective against broad attack patterns, but it can’t see inside the application logic of a specific plugin. Plugin-level solutions like Patchstack operate at the application layer, deploying targeted mitigation rules for specific plugin vulnerabilities. The most robust security posture combines both: network-level protection from the host, and application-layer protection from a tool like Patchstack. Neither replaces the other.
By making their security posture explicit and testable rather than assumed. That means clearly defining what they accept responsibility for at the infrastructure layer, being able to name their relationships with security intelligence companies, and having a documented incident response process they can walk a customer through before anything goes wrong.
