AI WordPress Security: How Agencies Can Protect Client Sites in 2026
AI WordPress security in 2026: 46% of vulnerabilities have no patch at disclosure. Here's what agencies need to protect client sites before attackers strike

AI has changed how WordPress sites are attacked, and how fast. According to Patchstack’s 2026 State of WordPress Security report, the median time to mass exploitation for high-impact vulnerabilities is just 5 hours. Meanwhile, 46% of plugin vulnerabilities don’t receive a patch by the time they’re publicly disclosed. This article explains how AI is reshaping the WordPress threat landscape, what that means for agencies managing multiple client sites, and what a practical, scalable security infrastructure looks like in 2026.
For most of WordPress’s history, security was a reactive discipline. A vulnerability gets disclosed, a patch gets released, and an agency eventually applies the update. That workflow was imperfect, but it more or less kept pace with how attacks happened. Humans were finding exploits and deploying them, and the timelines involved gave site managers some room to breathe.
That’s no longer true. AI has shifted how attacks are initiated, scaled, and targeted. One in six breaches online now involves an AI-driven component. For agencies managing dozens or hundreds of client sites, the old assumption that staying reasonably up to date is enough needs revisiting.
How AI-powered attacks target WordPress sites
The most consequential shift isn’t AI writing better malware. That’s just one part of the problem. According to the latest Patchstack report with Monarx, attackers have become more strategic and sophisticated in their methods, and malware is getting harder to find and even harder to remove.
However, the most consequential shift isn’t AI writing better malware. It’s AI enabling attackers to operate at a scale that wasn’t previously possible without substantial resources. An estimated 97% of WordPress attacks are already automated, AI is making those automated attacks faster, smarter, and harder to block.
Attackers are using bots and machine learning to scan thousands of WordPress sites in seconds, checking plugin versions, theme files, and server configurations against known vulnerability databases. Most plugin vulnerabilities can be exploited using fully automated, large-scale attacks with no prior access to the site required, and over half require no authentication at all. So, any site running an unpatched plugin isn’t just theoretically at risk; it’s practically to be discovered and probed quickly after a vulnerability is made public.
Brute force attacks tell a similar story. According to Limit Login Attempts Reloaded’s 2025 State of Brute Force Attacks report, brute force attacks on WordPress sites surged 130% in 2024, with attacks per domain up 120%. AI is a direct contributor: machine learning models can now crack over half of common passwords almost instantly, and even 7-character passwords with mixed complexity can be broken in under six minutes. Simple IP-based blocking is increasingly ineffective as bots distribute attempts across thousands of IPs; behavior-based detection is becoming a more reliable defense.
The credential stuffing problem compounds this. Attackers routinely take leaked username and password databases from breaches on other platforms and run them against WordPress admin logins at scale. For agencies managing client sites where they don’t fully control password hygiene across all users, this is a meaningful and ongoing exposure.
The biggest AI WordPress security risk for agencies
Despite the growing sophistication of AI-assisted attacks, the most exploited vulnerability in the WordPress ecosystem remains a simple operational failure: the gap between when a vulnerability is disclosed and when sites actually get protected.
According to Patchstack, the median time to mass exploitation for heavily exploited vulnerabilities is just 5 hours. That’s the window agencies are working with. Not days. Hours.
What makes this harder is that the patch isn’t always available in time. Patchstack’s data shows that 46% of plugin vulnerabilities did not receive a fix from the developer before public disclosure. That means agencies managing client sites can face a situation where a vulnerability is public, attackers are actively exploiting it, and there is no official update to apply.
For agencies managing 50 or 100 sites, this problem compounds quickly. Applying updates manually, even with reasonable diligence, creates uneven coverage. Some sites get patched same-day, others slip to the following week’s maintenance cycle. The sites that wait are the ones that get compromised. And when the patch doesn’t exist yet, manual updates aren’t even an option.
This is the core infrastructure problem that AI-powered attacks expose. Attackers don’t need to be clever when they can be fast and comprehensive. The defense isn’t to outthink them but to close the window before they reach it.
WordPress plugin vulnerabilities in the age of AI
The numbers from Patchstack’s 2026 report are stark. 11,334 new vulnerabilities were found in the WordPress ecosystem in 2025, a 42% increase over 2024. 91% of those vulnerabilities were in plugins, not core. And the severity picture is getting worse: highly exploitable vulnerabilities increased 113% year-on-year, meaning more vulnerabilities discovered in 2025 than in the previous two years combined had a high risk of mass-scale exploitation.
One finding worth understanding for agencies managing client sites across premium plugins and themes: 76% of vulnerabilities found in premium WordPress components were exploitable in real-life attacks. Premium plugins often get less security scrutiny because their code isn’t as readily available to researchers, which makes them a growing blind spot.
The practical implication is that vulnerability management needs to move from a manual task to a monitored infrastructure. Knowing which plugins are installed across your client sites, which ones have known vulnerabilities, and how severe those vulnerabilities are is the baseline. AI-powered scanners on the attacker side make patchwork awareness on the defense side insufficient.
What AI security means for WordPress agencies
The security industry has been quick to slap an AI label on anything with a detection algorithm, so it’s worth being precise about where AI genuinely adds value in the WordPress context.
Behavior-based threat detection is one area. Rather than matching traffic against a static list of known bad signatures, which attackers can trivially circumvent, behavior-based systems identify anomalies: login attempts that look statistically unusual, traffic patterns inconsistent with legitimate users, file changes that don’t correspond to scheduled updates. This is more robust against zero-day exploits because it doesn’t depend on having seen the attack before.
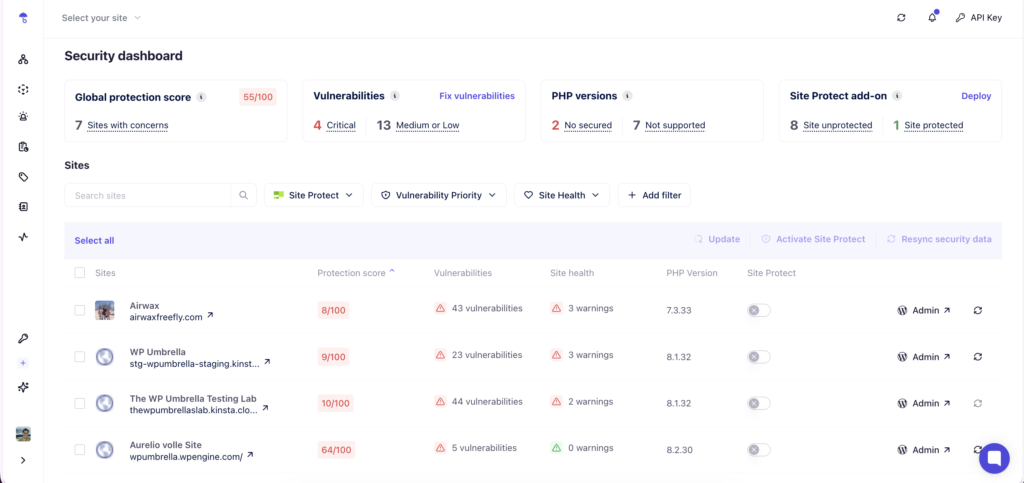
Automated vulnerability prioritization is another. Not every plugin vulnerability warrants an emergency response. AI-assisted severity scoring, weighing CVSS scores against factors like active exploitation in the wild, plugin install count, and authentication requirements, can help agencies triage their response and focus effort on important issues first. Patchstack’s own Priority Score system does exactly this, adjusting severity ratings based on real-world exploitability rather than raw CVSS scores alone.
Virtual patching to close the WordPress security window
One concept worth understanding in the context of AI-accelerated attack timelines is virtual patching. For agencies managing sites where immediate plugin updates aren’t always feasible, virtual patching offers a meaningful intermediate layer of protection.
Virtual patching works at the PHP level, intercepting requests that attempt to exploit known vulnerability patterns before they reach the vulnerable code. When a vulnerability is disclosed, and a patch isn’t yet available, or when applying the update immediately would require testing time, a virtual patch can block exploitation attempts without touching the plugin itself.
For agencies, the value is in the timing. If attackers begin scanning within 4 hours of a vulnerability disclosure and your normal patching cycle runs weekly, virtual patching covers the gap. It’s not a substitute for updating, but a bridge that keeps sites protected while the proper fix is applied.
Tools like Patchstack (which powers vulnerability scanning in WP Umbrella) maintain databases of virtual patches for disclosed WordPress vulnerabilities, applying them automatically when new vulnerabilities are published. This is the kind of infrastructure layer that makes a genuine difference at scale.
Your client sites are exposed the moment a vulnerability goes public. Site Protect closes that window automatically.
Site Protect is WP Umbrella‘s security add-on powered by Patchstack. It applies virtual patches at the PHP level, blocking known exploits for vulnerable plugins and themes in real time, even before an official update is available. No files are modified, no settings to configure, and zero impact on frontend performance. Just toggle it on from your WP Umbrella dashboard, and every connected site is protected instantly.
It also applies security hardening rules that stop common attack vectors automatically: user enumeration, XML-RPC abuse, file access probes, and more. Rules are continuously updated from Patchstack’s threat database, so your sites stay covered as new vulnerabilities emerge.
How to build WordPress security infrastructure that scales
Individual security measures, including 2FA, strong passwords, SSL, and reputable plugins, are necessary but not sufficient for agencies managing multiple client sites. The challenge at scale is executing it consistently across an entire portfolio without it consuming disproportionate time.
The agencies that handle this well tend to share a few operational characteristics. They use tools like WP Umbrella to:
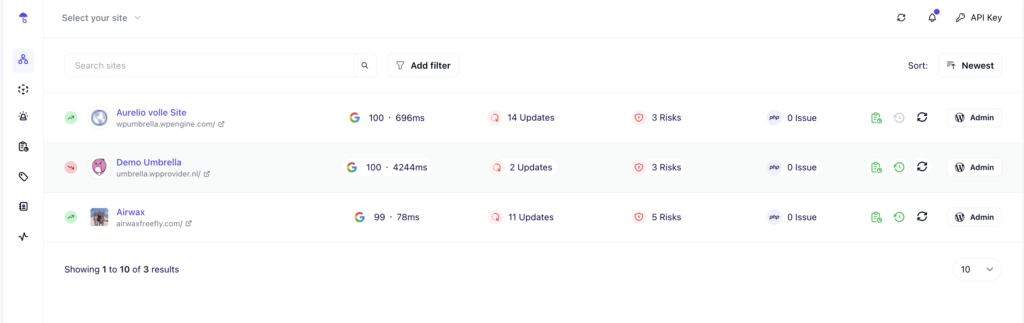
- Centralize visibility, using a single dashboard to monitor plugin versions, vulnerability alerts, and uptime across all sites rather than logging into each one individually.
- Automate the routine, trusted plugin updates applied automatically, with rollback capability if something breaks.
- Treat security as infrastructure rather than a project, meaning it runs continuously in the background rather than being addressed in response to incidents.
93% of security professionals now favor integrated platforms over point products. The same logic applies to WordPress site management. Fewer tools, better coverage, and cross-domain visibility between vulnerability monitoring, uptime, and performance outperform a stack of individual plugins addressing each concern in isolation.
For agencies auditing their current approach, the question worth asking is whether the tools you use give you accurate, centralized information about the state of your entire client portfolio at any moment, and whether your response to a critical vulnerability disclosure can realistically beat a 5-hour exploitation window.
Conclusion
AI hasn’t made WordPress security impossibly complex. It has made speed and consistency more important than they’ve ever been. WordPress agencies in 2026 will have to move security from a reactive task to a running infrastructure. One that doesn’t depend on someone noticing a problem before it becomes a breach.
WP Umbrella provides centralized vulnerability monitoring and automated update management for agencies managing multiple WordPress sites, with security scanning powered by Patchstack.
FAQs about AI WordPress security
AI is used to automate and scale attacks that were previously manual and slow. AI-driven scanners probe thousands of WordPress sites simultaneously, checking plugin versions and server configurations against known vulnerability databases within minutes of a new exploit being published. AI-powered botnets run credential prediction attacks and generate phishing content sophisticated enough to bypass traditional spam filters.
The exploitation window. Patchstack’s 2026 State of WordPress Security report states the median time to mass exploitation for high-impact vulnerabilities is 5 hours. What makes this harder for agencies is that 46% of plugin vulnerabilities don’t have a patch available at the time of public disclosure, meaning even a diligent agency following best practices may have no update to apply when a vulnerability goes public. Virtual patching is increasingly the only viable defense in that window.
Virtual patching is a security layer that intercepts and blocks exploit attempts at the application level, before they reach vulnerable plugin or theme code. When a vulnerability is disclosed, and a plugin patch isn’t yet available, which happens in nearly half of all cases, a virtual patch blocks attacks targeting that vulnerability without modifying the plugin itself. For agencies managing multiple client sites, it covers the window between disclosure and patching, which is when the majority of AI-driven exploitation occurs.
The key is moving from manual awareness to monitored infrastructure. This means using tools like WP Umbrella to maintain a centralized view of all plugins installed across client sites, receive real-time alerts when a plugin on any site has a disclosed vulnerability, prioritize patches based on severity and active exploitation data, and use virtual patching to cover the gap when immediate updates aren’t possible, or don’t exist yet. Agencies managing 50+ sites cannot reliably do this manually; it requires tooling that aggregates this information across the entire portfolio automatically.
In terms of the threat environment, yes. AI has accelerated the speed and scale of attacks in ways that manual security management struggles to keep up with. But the operational response is less about sophistication than consistency. Agencies that centralize their vulnerability monitoring, automate routine updates, and have protection in place that operates faster than a 5-hour exploitation window are well-positioned regardless of how attack tooling evolves. The fundamentals remain the fundamentals. AI just makes executing them more urgent.
